Computers | Free Full-Text | A Fast Text-to-Image Encryption-Decryption Algorithm for Secure Network Communication

An efficient public-key searchable encryption scheme secure against inside keyword guessing attacks - ScienceDirect
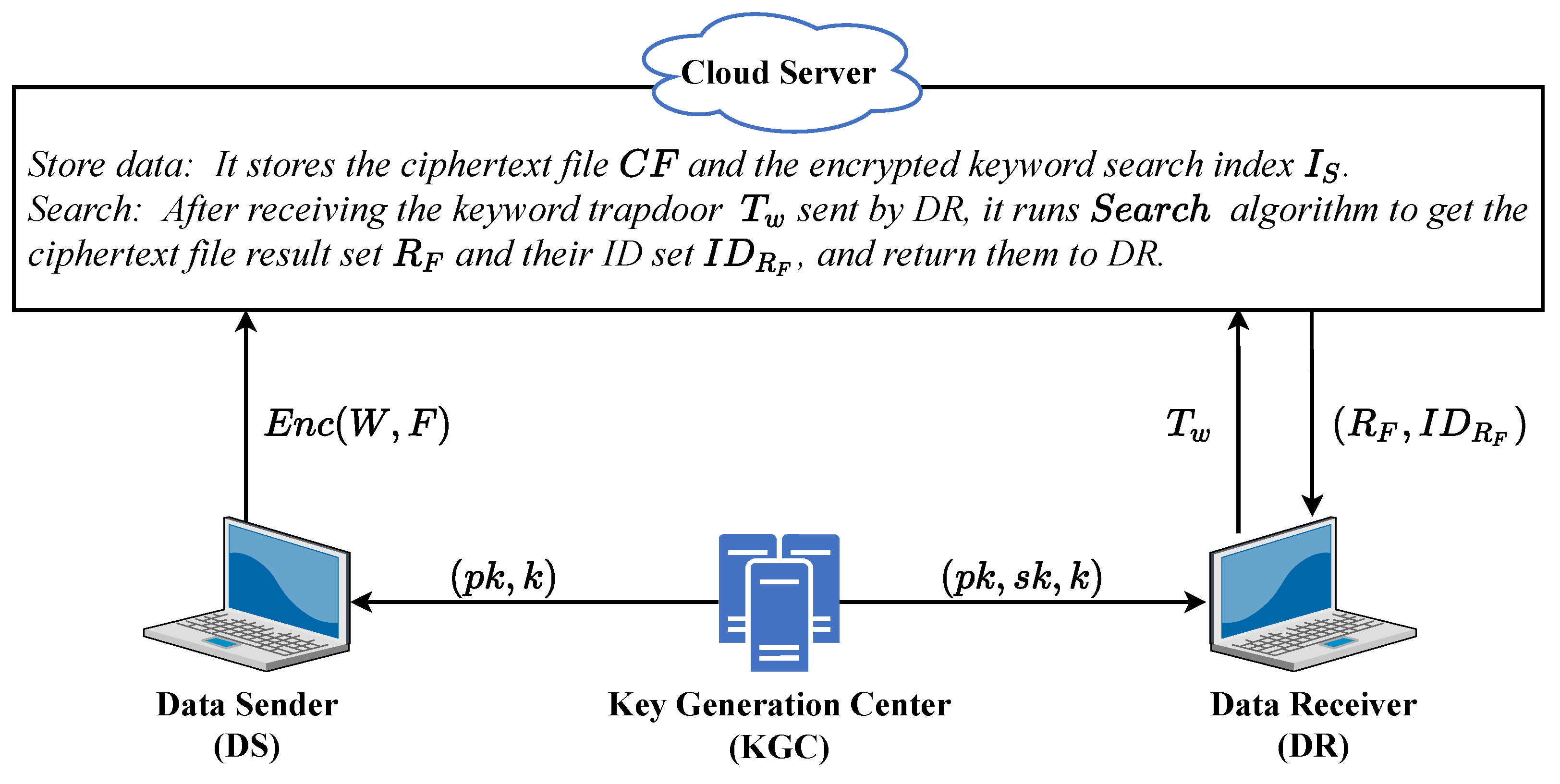
Applied Sciences | Free Full-Text | VR-PEKS: A Verifiable and Resistant to Keyword Guess Attack Public Key Encryption with Keyword Search Scheme